Hacker News Daily — 2026-05-01 Daily Best
🎧 Daily Podcast (English) — May 01, 2026
(1) Why does it take so long to release black fan versions?
Manufacturing a black edition requires retooling lines, requalifying components, and coordinating color coatings with supply chains, QA, and certification work. That combination slows the release cadence even as base models ship.
黑色版风扇的推出需要在制造线上进行重新布置、重新进行组件认证,并协调涂层、原料与供应链等环节,再加上严格的质量检测与认证流程。这些综合因素使得新版本的上市节奏明显慢于原厂标准款。
Ask.com has closed its consumer site, signaling another shift in the crowded search-engine landscape. The closure underscores how consolidation and monetization pressures reshape long-standing players in the space.
Ask.com 已关闭消费者网站,标志着搜索引擎领域再次洗牌。该举动反映出市场对可持续商业模式与资源配置的持续压力,以及行业格局的加速整合。
(3) Ti-84 Evo

Texas Instruments unveils the TI-84 Evo, a refreshed TI-84 graphing calculator aimed at students. It aims to deliver a snappier experience and better usability to keep calculators relevant in a classroom with modern devices. The update signals continued refinement of educational hardware rather than a switch to entirely different devices.
德州仪器推出 TI-84 Evo,作为 TI-84 图形计算器系列的更新版本,瞄准学生市场。新机型力求提升运行体验和可用性,使在使用笔记本和平板的课堂环境中,计算器仍具相关性。此次更新体现了教育硬件的持续改进,而非转向完全依赖其他设备。
(4) The gay jailbreak technique (2025)
A GitHub doc exposes a jailbreak technique named 'The Gay Jailbreak' that demonstrates prompt-injection and safety bypass methods for large language models. It underscores the ongoing arms race between researchers strengthening AI safety and attackers probing guardrails, with implications for defense and policy.
一份 GitHub 文档披露了名为“The Gay Jailbreak”的越狱技术,展示了通过提示注入绕过大型语言模型安全机制的方法。它凸显了AI 安全研究与对抗之间的博弈,以及对防御与政策的持续影响。
(5) Job Postings for Software Engineers Are Rapidly Rising
Global demand for software engineers is climbing as companies accelerate digitization and AI integration, driving more postings and competition for talent. The momentum suggests both higher salaries and greater scrutiny of candidates' portfolios and practical impact.
随着企业加快数字化转型与人工智能落地,对软件工程师的需求持续上升,招聘数量增加,行业竞争加剧。这一趋势往往伴随更高薪资与对实际能力的更严格评估。
(6) City Learns Flock Accessed Cameras in Children's Gymnastics Room as a Sales Demo

City learned that Flock cameras accessed cameras in a children's gymnastics room as a sales demo, raising privacy and governance concerns for surveillance tech vendors.
市政府发现 Flock 摄像头在儿童体操房被用作销售演示时访问摄像头,引发对监控技术供应商隐私与治理的担忧。
(7) New research suggests people can communicate and practice skills while dreaming
.jpeg)
New research finds that people may practice skills and even engage in brief communication while dreaming, suggesting sleep can support learning in ways previously underestimated. The results raise questions about how to harness dream-based rehearsal and what it means for education and memory consolidation.
新研究发现,人在做梦时可能练习技能、甚至与梦中人物短暂交流,说明睡眠也能以意想不到的方式促进学习。研究结果提出如何利用梦境中的演练来提升教育效果与记忆巩固的问题。
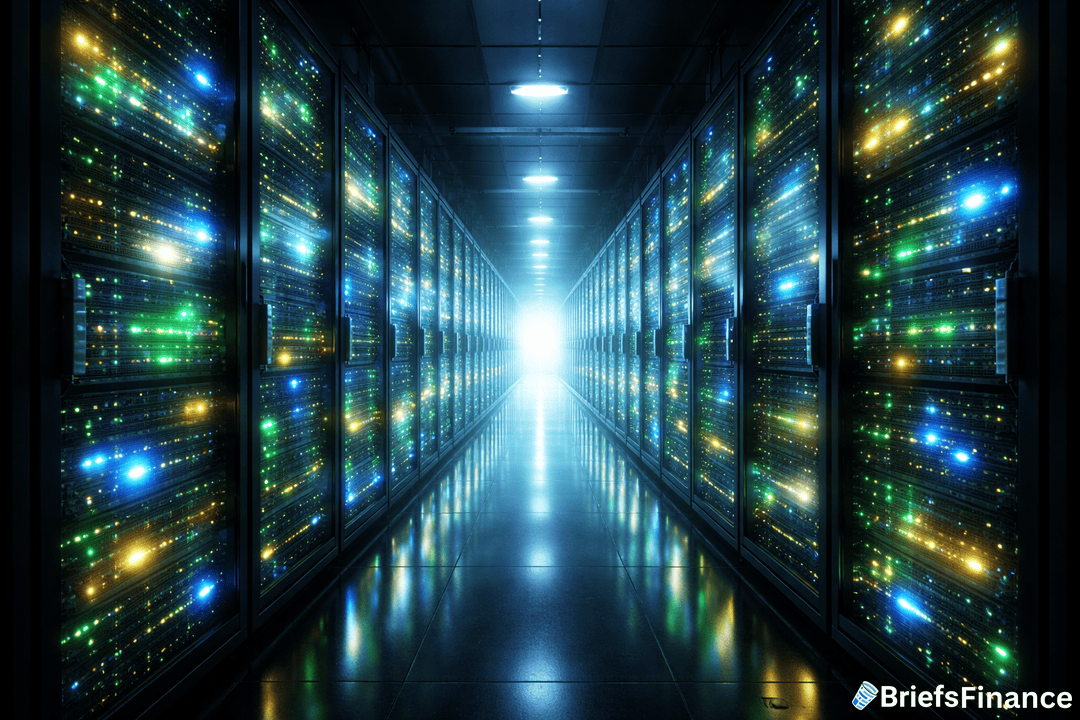
(8) AI uses less water than the public thinks
A California Water Blog post argues AI water use is smaller than common perception, despite AI's energy footprint. It dives into cooling practices, water recycling, and regional policy implications for water-scarce states, urging nuance in water-footprint accounting as AI expands.
加州水资源博客指出,尽管 AI 能耗很高,人工智能的数据中心用水量往往低于公众想象。文章探讨制冷方法、水循环再利用以及对水资源紧张地区的政策影响,强调在 AI 规模扩大时需要更精细的用水足迹核算。
(9) Uber torches 2026 AI budget on Claude Code in four months
Uber dramatically front-loads its AI investment, dedicating the entire 2026 budget to Claude Code for four months. This signals a push to accelerate internal AI-assisted coding, potentially reshaping its software-dev workflows and cost structure.
优步将在四个月内把2026年的AI预算全部投向Claude Code,提前放大对AI辅助编码的投入。这举措旨在加速内部开发流程,但也意味着成本压力和对 Claude Code 的高度依赖。
(10) Claude Code refuses requests or charges extra if your commits mention "OpenClaw"

Claude Code reportedly refuses or incurs extra charges for requests tied to the phrase OpenClaw, illustrating guardrails around prompts and naming in coding assistants. The detail reflects how policy constraints and pricing are implemented in AI development tools.
报道称 Claude Code 对提及 OpenClaw 的提交拒绝请求,甚至额外收费,体现对特定提示的安全与定价策略在编码助手中的应用。
(11) Credit cards are vulnerable to brute force kind attacks
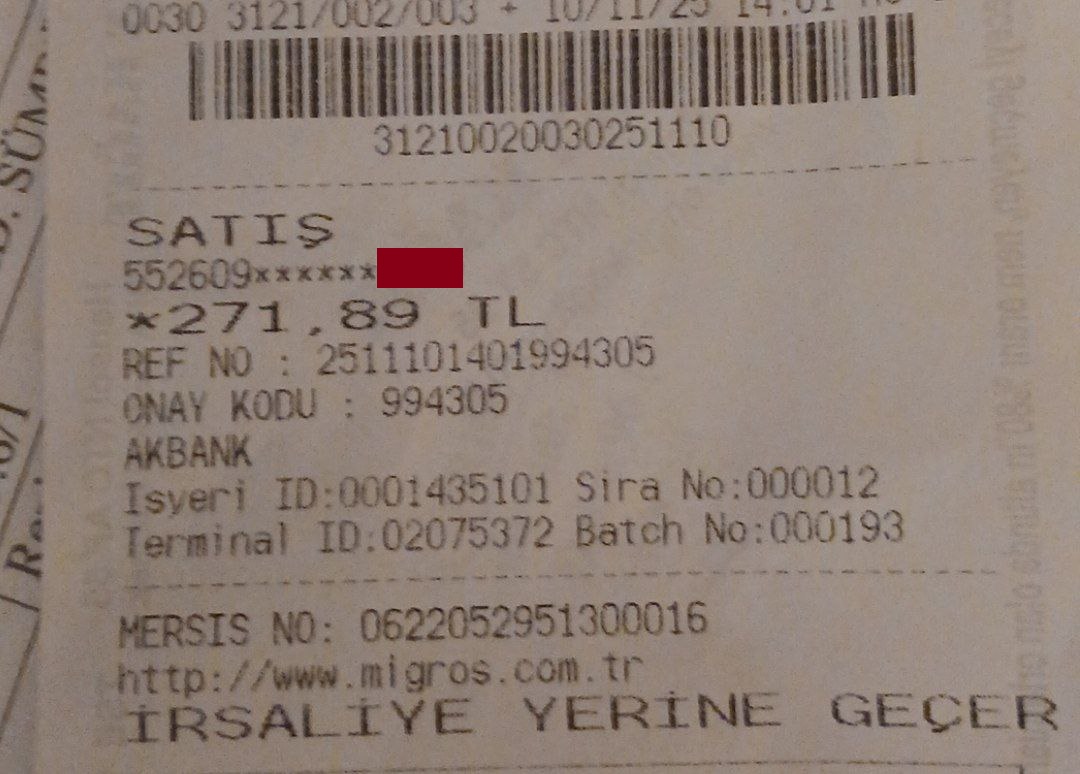
A security analysis shows that some card-processing setups can be exploited via offline brute-forcing of card numbers, enabling attackers to test large candidate pools until a valid number is found. The finding underscores the need for strong rate limiting, tokenization, and robust verification to prevent fraud in both card-present and online contexts.
安全分析显示,某些信用卡处理流程在离线环境下可能被暴力穷举卡号,攻击者可测试大量候选号码直至找到有效卡。这一发现凸显对速率限制、令牌化和强健验证的需求,以防止实体和在线交易中的欺诈。
(12) Show HN: WhatCable, a tiny menu bar app for inspecting USB-C cables
WhatCable is a tiny macOS menu-bar app that inspects USB-C cables to report capabilities like power delivery and alt-mode support. It demonstrates how lightweight utilities can help developers verify hardware compatibility.
WhatCable 是一个极简的 macOS 菜单栏应用,可检查 USB-C 电缆的供电、替代模式等能力,帮助开发者快速核对硬件兼容性。
(13) Apple accidentally left Claude.md files Apple Support app

A misconfiguration exposed Claude.md files in the Apple Support app. The files could reveal sensitive information about Claude integration or internal workflows, highlighting how even large platforms can leak developer docs if not careful.
一个错误配置让 Apple Support 应用中暴露了 Claude.md 文件,可能泄露关于 Claude 集成的内部文档和工作流信息。这再次暴露了大型应用中的隐私与安全漏洞,以及加强访问控制的必要性。
(14) Police Have Used License Plate Readers at Least 14x to Stalk Romantic Interests
At least 14 documented instances where police used license plate readers to stalk romantic interests. The report highlights civil-liberties risks and underscores the need for guardrails on surveillance tech, including access controls, data retention, and purpose limitation.
据报道,警察至少在14起案件中利用车牌识别系统来监视恋爱对象。这暴露出监控技术在个人私隐领域的滥用风险,呼吁对数据用途、保留期限和访问权限设定更严格的规范。
(15) Spotify adds 'Verified' badges to distinguish human artists from AI

Spotify adds Verified badges to differentiate human artists from AI-generated content, signaling a move toward transparency in streaming metadata and potential new monetization rules.
Spotify 推出 Verified 徽章以区分真人艺人与 AI 生成内容,表明在流媒体元数据透明度方面向前迈出一步,并可能引入新的货币化规则。
(16) Ask HN: Who is hiring? (May 2026)
A Hacker News community-sourced roundup of open roles for May 2026. Expect startups and tech firms listing software, data, and engineering roles, with an emphasis on remote work and competitive compensation.
这是 Hacker News 社区整理的五月 2026 年开放岗位汇总,覆盖初创公司与科技企业的软件、数据与工程类职位,重点关注远程工作与有竞争力的薪酬。
(17) Can I disable all data collection from my vehicle?

Car makers generally allow opting out of some data collection, but completely disabling telemetry is often not possible due to safety, features, and updates. The Rivian guidance illustrates what can be turned off and what remains required for core functions like safety and navigation.
多数车企允许关闭某些数据收集,但完全禁用遥测往往因安全性、功能性和更新需求而受限。Rivian 的指南显示哪些数据可以关闭、哪些仍然被收集用于安全与导航等核心功能。
(18) Grok 4.3
Grok 4.3 is the latest release of the Grok model family, offering updates to its model API and capabilities for developers building on the platform.
Grok 4.3 是 Grok 模型家族的最新版本,为在该平台上构建应用的开发者带来 API 与能力的更新。
(19) An open letter asking NHS England to keep its code open
An open letter urging NHS England to keep its software open-source, arguing openness improves security, interoperability, and accountability in health tech.
公开信呼吁 NHS England 保持代码开源,主张开放性可提升安全性、互操作性和对健康科技开发者及患者的问责性。
(20) DeepSeek V4–almost on the frontier, a fraction of the price

Simon Willison’s DeepSeek V4 release promises near-frontier capabilities at a fraction of the cost, highlighting ongoing trends in accessible, high-performance search tooling for developers.
Simon Willison 介绍的 DeepSeek V4 在成本极低的前提下接近前沿能力,凸显开发者对高性能、可负担的搜索工具的持续需求。文中评测、功能要点及与主流方案的取舍成为技术选型的参考。
(21) Apocalypse Early Warning System
A project for real-time, global catastrophe early warning using data fusion and alerting; discusses how citizens and systems should respond to existential threats.
一个基于数据融合的全球实时灾难预警系统,探讨公民与系统应对严重威胁的方式与治理。
(22) The X-Files has made me nostalgic for a time I never experienced
The piece reflects on how The X-Files stirs nostalgia for a tech-era people never experienced, shaping attitudes toward mystery, data, and surveillance today. It uses fan nostalgia to comment on media influence and the evolution of tech culture.
作者通过《X档案》唤起对未曾经历过的上世纪科技与社会氛围的怀念,进而反思当代对数据、监控和隐私的认知。文章借助流行文化的怀旧感,探讨媒体如何塑造我们对技术时代的想象。
(23) Flock cameras keep telling police a man who doesn't have a warrant has a warrant
A video shows Flock cameras repeatedly flag a man as having a warrant, despite no warrant in reality. This highlights the risks of automated surveillance tools misidentifying individuals, potentially leading to wrongful police action and civil-liberties concerns.
视频显示 Flock 的摄像系统反复将一名无逮捕令的男子错误标记为有逮捕令。这凸显了自动化监控工具在识别个人时可能产生的误判,带来潜在的权利侵害与滥用风险。
(24) Lib0xc: A set of C standard library-adjacent APIs for safer systems programming
Lib0xc provides a set of C standard library-adjacent APIs that emphasize safety for systems programming, with bounds-checked routines and safer defaults to reduce memory-safety risks while staying compatible with existing C code.
Lib0xc 提供一组接近 C 标准库的更安全 API,聚焦在边界检查和更安全的默认行为,帮助降低系统编程中的内存安全风险,同时尽量保持与现有代码的兼容性。
(25) How Mark Klein told the EFF about Room 641A [book excerpt]
Mark Klein, a former AT&T technician, disclosed to the EFF the existence of Room 641A, a secret facility where fiber-optic lines were allegedly tapped for mass surveillance. The excerpt presents his firsthand account and the ensuing controversy, showing how insider disclosures can catalyze public scrutiny and policy debate around surveillance. It underscores the lasting impact whistleblowers have on privacy advocacy and reform efforts.
前 AT&T 技术员 Mark Klein 向电子前哨基金会披露了“641A 室”的存在,据称在那里对光纤线路进行了大规模监控拦截。书摘给出他的第一手叙述及随后的争议,展示了内部披露如何点燃公众关注并推动 surveillance 相关的政策辩论。此事凸显举报人在隐私倡议与改革中的长期影响。
(26) Your website is not for you
The article argues that building a website should center on users, not the creator's preferences. It emphasizes clear messaging, performance, and easy navigation, with practical steps for designers and developers.
文章强调网站应以用户为中心,而非追随创作者的喜好。通过明确信息传达、提升性能与可用性,给设计与开发者提供了落地的建议。
(27) For Linux kernel vulnerabilities, there is no heads-up to distributions

Linux kernel vulnerability disclosures often fail to provide a formal heads-up to distributions, delaying patch adoption. The situation highlights gaps in how advisories propagate from researchers to downstream users, affecting enterprise risk management.
Linux 内核漏洞的披露往往没有直接向发行版提供正式的事先通知,导致修补落地延迟。这暴露了研究人员、公告渠道与发行版维护之间的信息传递断层,影响企业的风险管理和修补节奏。
(28) AWS stops billing Middle East cloud customers as repairs to war damage drag on

Amazon Web Services paused billing for Middle East cloud customers due to ongoing repairs from war damage to data centers, extending the disruption for clients relying on regional services. The incident highlights how geopolitical conflict can ripple into cloud economics and service continuity, prompting questions about resilience and billing transparency.
亚马逊云服务因战争造成的数据中心损坏仍在修复中,暂停对中东地区云服务客户的计费。此举暴露出地缘政治冲击对云服务、运营成本和计费透明度的影响,凸显对韧性和客户沟通的需求。
(29) I'm Peter Roberts, immigration attorney who does work for YC and startups. AMA
Peter Roberts, an immigration attorney who works with YC and startups, hosts an AMA about visas, sponsorship pipelines, and global hiring realities for startups.
Peter Roberts 这位为 YC 与初创公司提供移民法律服务的律师开启 AMA,解答签证选项、赞助流程及全球招聘中的现实挑战。
(30) Understand Anything
Understand Anything is a project aiming to build a broad reasoning interface to demystify complex concepts and code across domains. It explores universal explainability tooling and cross-domain collaboration.
Understand Anything 项目旨在构建一个广域推理界面,以跨领域解释复杂概念与代码。它探索普适的可解释性工具以及跨领域协作的可能。
(31) Spain's parliament will act against massive IP blockages by LaLiga
Spain's parliament plans to curb mass IP blockades pushed by La Liga, addressing concerns over overbroad blocks that can affect legitimate sites. The move signals a push for more measured, privacy-respecting enforcement while preserving anti-piracy aims. It highlights the tension between content protection and civil liberties in digital policy.
西班牙议会计划限制 La Liga 推动的广泛 IP 阻断措施,纠正对合法站点和服务的过度封锁。此举旨在在实现反盗版目标的同时,推动更克制、尊重隐私的执法方式。
(32) LinkedIn is scanning browser extensions

LinkedIn reportedly scans installed browser extensions to detect abuse and improve security. The practice could allow LinkedIn to collect details about extensions and usage patterns, raising privacy concerns about data handling and potential sharing.
LinkedIn 据称会扫描用户安装的浏览器扩展以检测滥用并提升安全性。这一做法可能让 LinkedIn 收集扩展信息和使用模式,引发对数据处理、存储与共享的隐私担忧。
(33) How an oil refinery works

An oil refinery uses distillation towers to separate crude oil into fuels and feedstocks, then refines these streams through cracking, reforming, and blending. The process is large-scale, energy-intensive, and central to energy economics, making understanding it valuable for anyone following infrastructure tech.
炼油厂通过塔式蒸馏等工艺把原油分离成燃料和化工原料,再经裂解、改质和混合进行深加工。这个过程规模庞大、能耗高,是能源经济的核心,理解其流程有助于把握能源市场的运行。
(34) Meta in row after workers who saw smart glasses users having sex lose jobs

Meta is at odds after reports that employees who witnessed colleagues using smart glasses to observe sexual activity were fired. The situation highlights tensions around wearable surveillance, employee reporting, and HR policies in a highly visible tech company.
据报道,Meta 团队中一些在目睹同事通过智能眼镜观看性行为后被解雇的员工,引发了关于穿戴式监控、举报流程与人力资源政策的争议。这一事件凸显了科技巨头在员工安全与隐私之间的博弈。
(35) Whohas – Command-line utility for cross-distro, cross-repository package search
whohas is a CLI tool to search packages across Linux distributions and repositories, streamlining compatibility checks for multi-distro environments. It helps developers quickly locate where a package exists and what version is available, reducing dependency guesswork.
whohas 是一个命令行工具,用于跨 Linux 发行版和仓库搜索软件包,简化多发行环境下的兼容性检查。它帮助开发者快速定位软件包的位置与可用版本,降低依赖猜测成本。
(36) Shai-Hulud Themed Malware Found in the PyTorch Lightning AI Training Library
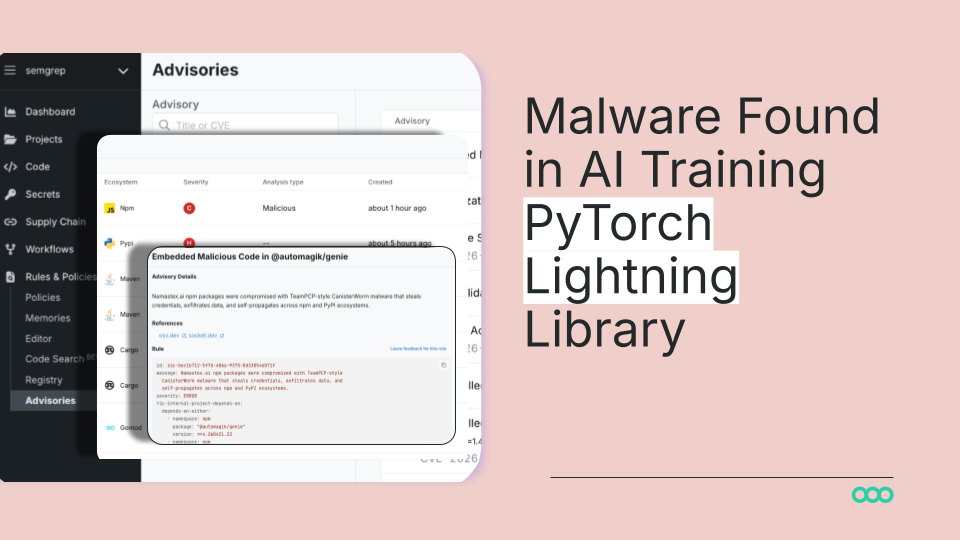
Researchers found a malware-laden dependency in the PyTorch Lightning AI training library, themed around Shai-Hulud from Dune. The incident highlights the ongoing supply-chain risk in ML tooling, where critical libraries can be hijacked or compromised. It emphasizes the need for strict dependency vetting, vendor auditing, and reproducible environments to keep ML workflows secure.
研究人员在 PyTorch Lightning 的 AI 训练库中发现了一个带有 Shai-Hulud 主题的恶意依赖。此事件暴露了机器学习工具链的持续供应链风险——核心库可能被劫持或被植入恶意代码。强调对依赖项的严格审查、供应商审核,以及可重复环境的重要性,以确保 ML 工作流安全。
(37) Running Adobe's 1991 PostScript Interpreter in the Browser
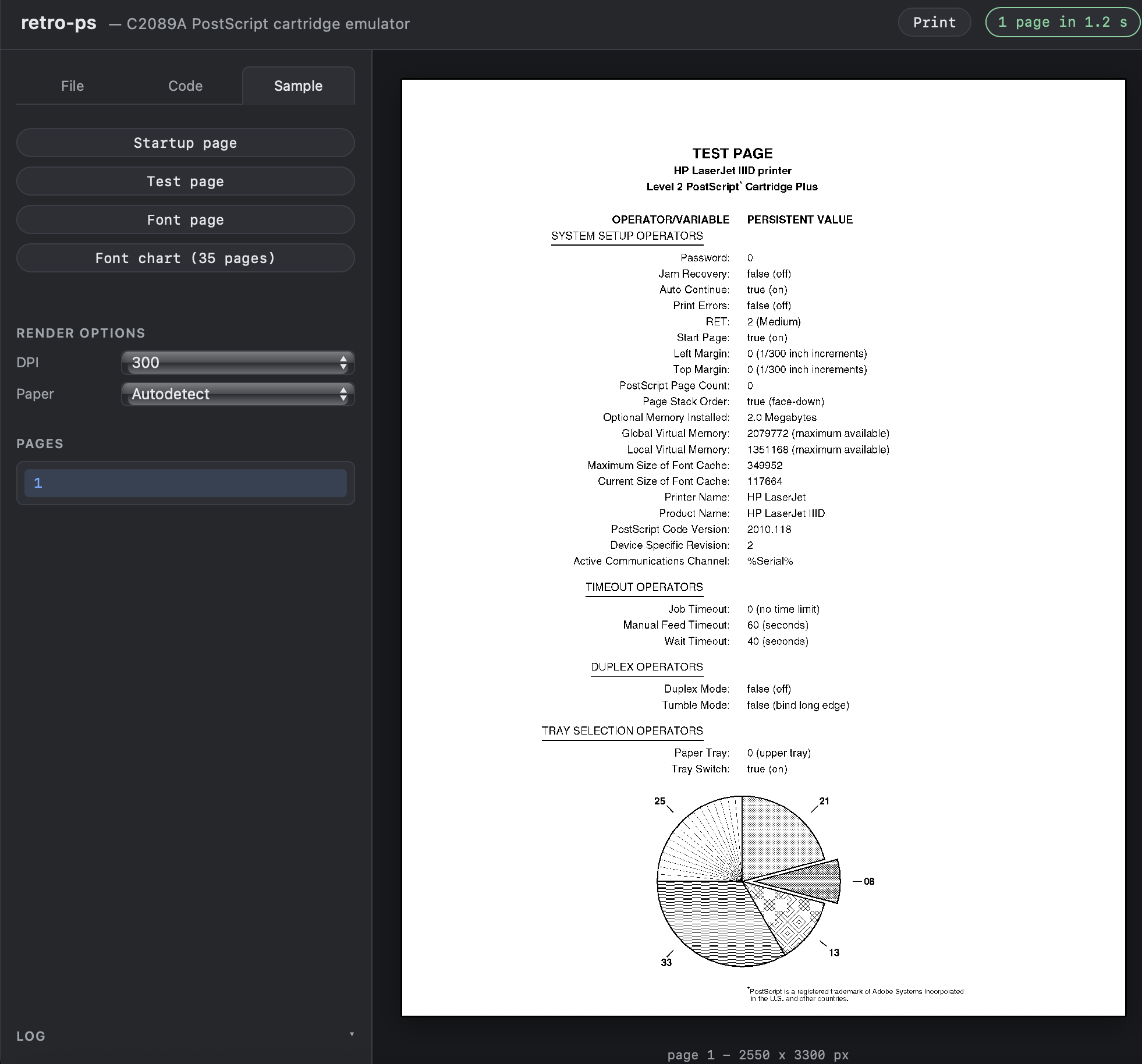
A project ports Adobe's 1991 PostScript interpreter to run in the browser, allowing faithful rendering of legacy PostScript documents without server-side tooling. It highlights the challenges of porting a vintage interpreter to modern environments and the performance/precision considerations involved. The effort underscores the value of emulation for digital preservation and retro computing.
一个将 Adobe 1991 年 PostScript 解释器移植到浏览器的项目,使老旧的 PostScript 文档能够在客户端渲染,避免对服务器端运行时的依赖。展示了把历史解释器带入现代运行时的挑战以及性能与精度的权衡。此工作凸显了在数字保存和复古计算领域,浏览器端仿真的重要性。
(38) Canonical/Ubuntu have been under DDoS
Canonical and Ubuntu infrastructure faced a sustained DDoS attack lasting more than 15 hours, disrupting services and user access. The incident underscores the need for robust DDoS defenses and incident response in high-visibility open-source ecosystems.
Canonical 与 Ubuntu 的基础设施遭受持续超过15小时的 DDoS 攻击,影响服务与用户访问。事件凸显在高可见性开源生态中部署强大防护和应急响应能力的重要性。
(39) U.S. Senators Vote to Ban Themselves from Trading on Prediction Markets
In a rare move, U.S. Senators voted to ban themselves from trading on prediction markets. The rule aims to curb conflicts of interest and insider-information concerns, though critics argue it may be inconsistent with broader market experimentation.
美国参议员投票禁止自己在预测市场进行交易,旨在降低利益冲突和内幕信息风险。批评者则质疑此类自我约束是否与更广泛的市场试验规则相一致。
(40) I built a Game Boy emulator in F#
I built a Game Boy emulator in F# from scratch, tackling the platform's timing, CPU, and memory quirks with a functional language. The project showcases how expressive, type-safe FP languages can still perform low-level emulation, and offers insights on bridging game architecture with modern tooling. It's a proof-of-concept that highlights the trade-offs between expressiveness and performance in hobby hardware emulation.
作者用 F# 从零开始实现了一个 Game Boy 模拟器,需处理时序、CPU 与内存等细节。这个项目展示了函数式语言在底层仿真中的可行性与权衡,给出在现代工具链下进行硬件仿真的经验与启示。
(41) After dissing Anthropic for limiting Mythos, OpenAI restricts access to Cyber

OpenAI tightened access to the Cyber model following public criticism of Anthropic's Mythos restrictions, signaling growing caution around model availability and safety policy. The move underscores the competitive tensions in AI developer ecosystems and how governance debates influence access to powerful tools.
OpenAI 在公开批评 Anthropic 对 Mythos 限制后,进一步收紧对 Cyber 模型的访问,显示出对模型可得性和安全政策的日趋谨慎。这凸显了 AI 开发者生态的竞争格局,以及治理议题如何影响对强大工具的访问。
(42) OpenWarp
OpenWarp appears to be an open-source project focused on warp-themed tooling.
OpenWarp 看起来是一个聚焦于 warp 相关工具的开源项目。
(43) I aggregated 28 US Government auction sites into one search
I aggregated 28 US government auction sites into one search tool to simplify finding assets, surplus equipment, and procurement opportunities. The project illustrates the value of unifying public-data sources to boost efficiency, while data freshness and reliability remain important.
作者把 28 个美国政府拍卖网站聚合为一个检索入口,便于发现资产、闲置设备与采购机会。此举体现整合公开数据源以提升效率的趋势,但数据的时效性与可信度同样重要。
Vercel's pricing page is under scrutiny for how it's structured—potential changes around free tier, team plans, and build-time costs. The analysis compares value and predictability for startups choosing a hosting/edge platform.
对 Vercel 定价结构的评估揭示了免费层、团队计划与构建成本等方面的潜在变化与误解。该分析帮助初创公司在选择托管/边缘计算平台时评估价值与可预测性。
(45) Honker – Durable queues, streams, pub/sub, and cron scheduler in a SQLite file

A single SQLite file can host durable queues, streams, pub/sub, and a cron-like scheduler, enabling complex data workflows without external services. This approach can be appealing for edge apps or offline-first systems.
一个 SQLite 文件就能承载持久化队列、流、发布/订阅和类似 cron 的调度功能,从而在不依赖外部服务的情况下实现复杂数据工作流。文中探讨如何在一个紧凑的数据存储中实现原语,权衡简单性与潜在的性能、可移植性之间的取舍,适合边缘计算或离线优先场景。
(46) Full-Text Search with DuckDB
A practical guide to enabling full-text search with DuckDB, outlining the setup, indexing strategies, and performance considerations. The piece demonstrates how embedded analytics databases can provide rich search capabilities without requiring separate search engines, useful for data apps and notebooks. It also notes caveats compared to dedicated search systems.
介绍在 DuckDB 中实现全文检索的实用指南,涵盖设置、索引策略及性能考量。展示了嵌入式分析数据库在无需独立搜索引擎的情况下提供丰富检索能力,对数据应用和笔记本场景尤为有用,同时也提醒了相对于专门的搜索系统的局限。
(47) Does Postgres Scale?
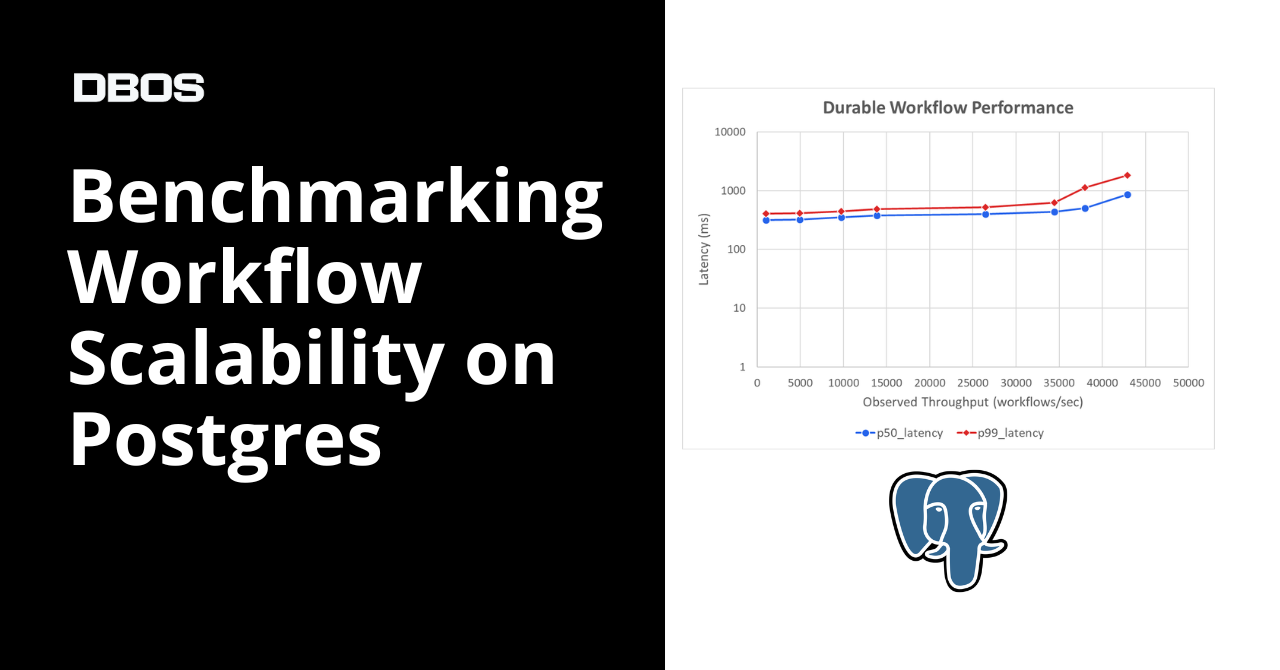
A benchmarking post measures workflow execution scalability on PostgreSQL, exploring how well it handles growing complexity and parallelism. The results suggest PostgreSQL can scale for certain workloads with careful design, but may hit limits without specialized architecture.
一篇基准测试文章评估 PostgreSQL 在工作流执行方面的扩展性,探讨其在日益复杂和并行化的任务中的表现。结论显示,在合适的设计下 PostgreSQL 可以在部分工作负载上实现可观的扩展性,但遇到极端规模时可能需要更专门的架构或工具。
(48) CPanel and WHM Authentication Bypass – CVE-2026-41940

A CVE-2026-41940 describes an authentication bypass in CPanel/WHM, potentially allowing attackers to access privileged accounts. The advisory urges upgrading to patched versions and applying mitigations; administrators should rotate credentials and review access controls.
CPanel/WHM 的身份验证绕过漏洞 CVE-2026-41940 已披露,可能使攻击者获取特权账户权限。建议尽快升级到修补版本并应用缓解措施,同时检查访问控制和凭据轮换。
(49) American Dads Became the Parents Their Fathers Never Were

Derek Thompson argues that richer dads are spending more time with their children than their own fathers did, reflecting debt of time and resources across generations. The piece analyzes how wealth, work flexibility, and social norms shape parenting, with implications for child development and family policy.
Derek Thompson 指出,富裕阶层的父亲花在陪伴子女上的时间增多,超过了他们父辈的水平。文章分析财富、工作灵活性和社会规范如何塑造育儿方式,并对儿童发展与家庭政策产生影响。
(50) U.S. Debt Tops 100% of GDP
The U.S. debt-to-GDP ratio has surpassed 100%, underscoring fiscal policy constraints and potential macroeconomic risks for higher interest payments and investment in tech.
美国债务与 GDP 比率超过 100%,凸显财政政策的约束和对更高利息支出及科技投资的潜在宏观风险。